Mandated by the FBI, compliance with the CJIS Security Policy is non-negotiable for law enforcement agencies and vendors that handle Criminal Justice Information (CJI). So, the question “why is CJIS compliance mandatory?” naturally comes up quite often.
The short answer is data security. As CJI databases contain highly sensitive information, the FBI places strict requirements for its protection. Mandatory CJIS compliance guarantees that sensitive data are secured throughout its entire lifecycle.
Regardless of whether you’re accessing NCIC, NLETS, state systems, or local repositories, agencies and vendors alike need to be CJIS-compliant. This is to ensure officer safety, public safety, and smooth agency operations, as well as to avoid legal liability. Failure to do so leads to an immediate loss of access to CJI databases.
This article clarifies the legal foundation of the mandatory CJIS standards for police work, its benefits, and the consequences of non-compliance. It also breaks down the CJIS requirements for law enforcement software, so that you can confidently choose one that genuinely safeguards your agency.

The Federal Mandate: Legal Foundation of CJIS Compliance Requirements
To understand why CJIS compliance is mandatory, it’s crucial to know the legal chain of authority from the federal statute through the FBI’s CJIS Division all the way down to state and local agencies. This isn’t just a “best practice” checklist. Rather, it’s a federal mandate backed by statute, policy, and formal governance structures.
The legal foundation starts with 28 U.S.C. § 534, which authorizes the FBI to collect, preserve, and exchange criminal identification and crime data. This authority fuels systems like the National Crime Information Center (NCIC) and other national crime databases. Because the FBI controls these systems, they also control the rules for accessing them.
Using that authority, the FBI’s Criminal Justice Information Services (CJIS) Division published the CJIS Security Policy. It provides a comprehensive security rulebook that defines everything from encryption and user authentication to personnel vetting and incident response. This policy is updated regularly as threats evolve.
Enforcement isn’t purely federal, either. The Compact Council, made up of state representatives, helps translate federal requirements into state-level governance. Each state appoints a CJIS Systems Officer (CSO) who enforces compliance among state, county, and local agencies. This creates a clear hierarchy: federal mandate to state enforcement to local compliance.
Access to FBI systems is conditional. Agencies must sign the Security Addendum, a legally binding agreement that makes mandatory CJIS standards for police explicit. No compliance means no access there are no carve-outs or “close enough” exceptions.
Importantly, third parties aren’t off the hook. Any vendor, cloud provider, or contractor touching Criminal Justice Information must follow the same rules. This ensures understanding and compliance of CJIS requirements for law enforcement applies across the entire ecosystem, not just sworn personnel.
In short: compliance isn’t optional it’s federal law with real operational consequences.
What Makes Police Software Subject to CJIS Compliance?
In considering CJIS requirements, law enforcement agencies and vendors need to evaluate their police software. According to the FBI’s Criminal Justice Information Services (CJIS) Security Policy, any system that has access to, stores, processes, or transmits Criminal Justice Information (CJI) needs to be compliant.
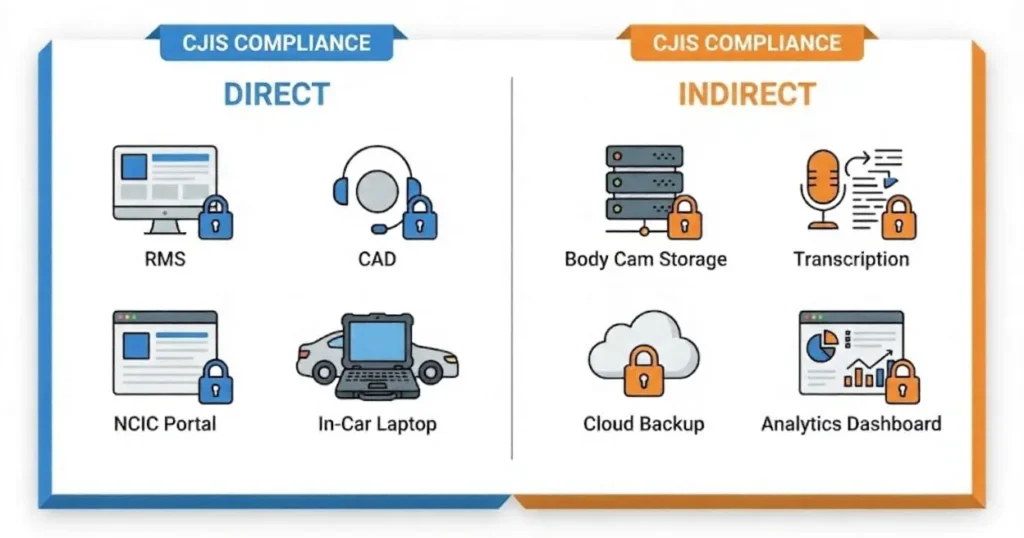
Almost all modern policing software accesses CJI in one way or another, either directly or indirectly.
Direct Access Systems
These systems can query, open, edit, and enter data directly into criminal justice databases. Real-time operations require direct access systems to manage CJI, and such systems are subjected to rigorous controls like encryption and audit logs:
- RMS (Records Management Systems): RMS serves as the repository for the police to save arrest records and incident reports that have CJI in their content.
- CAD (Computer-Aided Dispatch): CAD processing systems transmit CJI during emergencies along with the suspect detail calls.
- Database access portals (NCIC, NLETS queries): Officers get the information needed for warrants and stolen property checks by querying NCIC through authorized systems as per 28 U.S.C. § 534.
- Mobile data terminals and in-vehicle systems: Patrol cars use laptops or tablets connected to the national databases to access CJI.
- Evidence management systems: The CJI embedded in photos, videos, and documents is managed by these systems.
Indirect Access Systems
Indirect access systems interact with CJI secondarily, which means they can only view and collect CJI, and can’t make any modifications:
- Body camera footage storage: Videos that contain identifiable CJI need to be stored securely either in the cloud or on-premises.
- Transcription services: AI tools are used to process body cam audio that contains suspect statements or victim data.
- Cloud backup systems: All backups of files that bear CJI must comply with CJIS encryption standards.
- Case management platforms: Account for investigations with CJI references in different departments.
- Analytics and reporting tools: Collect statistics related to crime that come from CJI sources.
Both direct and indirect access systems require compliance. However, implementation differs, as direct access systems require stricter security measures and more frequent auditing than indirect access systems.
On a different note, software vendors and cloud services that deal with CJI in any way also need to comply with mandatory CJIS standards for police. If you’re unsure whether compliance is required or not, it’s best to assume that it is. Get in touch with your state CJIS Security Officer (CSO) for clear CJIS compliance guidance for police software.

Critical Consequences of Non-Compliance with Mandatory CJIS Standards
Non-compliance with mandatory CJIS standards for police leads to operational, legal, financial, and reputational consequences, putting agencies, officers, and communities at risk. Agencies must give top priority to CJIS compliance in order to protect Criminal Justice Information (CJI) and maintain the integrity of operations.
Immediate Operational Consequences
Agencies that do not comply with regulations will immediately lose their access to NCIC, NLETS, and state criminal databases. Agencies being cut off from essential intelligence will lead to them facing instant police work issues.
- Officer Safety Risks: Officers won’t be able to perform warrant checks, ID verifications, or stolen property checks during traffic stops, thus posing a threat to lives.
- Stalled Investigation: Active cases will be stalled due to a lack of access to criminal histories or fingerprint databases.
- Dispatch Disruption: During emergencies, 911 operators are unable to perform queries of databases, thus prolonging the responses.
- Inter-agency cooperation breakdown: Other agencies will not share CJI with non-compliant partners.
- Evidence compromised: If the evidence chains involve non-compliant systems, courts can dismiss cases.
Legal and Regulatory Consequences
Federal and state authorities enforce penalties when agencies violate the mandatory CJIS standards for police.
- Federal Penalties: Federal law can impose serious criminal penalties, including imprisonment and fines, on anyone who violates the 28 U.S.C. § 534 and related statutes.
- State-Level Sanctions: Each state has its own penalties, which include administrative sanctions, fines, or even temporarily closing the police department.
- Civil Liability: People whose CJI was wrongly accessed or disclosed can file lawsuits.
- Criminal Liability: Willful violation results in criminal charges against those responsible, such as IT personnel, chiefs, and administrators.
- Contract Violations: Loss of federal loans and state financing that are subject to compliance.
- Impacts on Vendors: Software vendors lose the credibility to serve the law enforcement market.
Financial Consequences
Non-compliance is expensive. If you’re an agency operating on tight budgets, you won’t want to face hefty remediation costs to fix gaps and meet mandatory CJIS standards. Failing to comply can slow down the police work, and those delays usually translate into higher operational expenses and project overruns.
- Breach Notification Expenses: Data incidents from non-compliance trigger mandatory reporting fees.
- Legal Defense Costs: Defending lawsuits and regulatory actions leads to high attorney and legal proceedings bills.
- Lost Productivity: Operations are severely disrupted or even completely stopped during the remediation period.
- Insurance Impacts: Premiums go up drastically, or the insurance is cut off because of non-compliance.
- Grant Ineligibility: You’ll miss federal and state funding, as most require CJIS compliance.
Reputational and Trust Consequences
Reputation and public trust are everything in public safety. But when an agency falls short of mandatory CJIS standards, it erodes confidence. Community members begin to question the agency’s technical skills and competency, while partner organizations may become more hesitant to collaborate.
- Media Scrutiny: The breaches maintain the headlines and damage the agency’s credibility in the long run.
- Recruitment/Retention Effects: The best workforce is not attracted to or is leaving the agencies that are not complying with the required standards.
- Inter-Agency Relationships Damaged: Data-sharing with neighbors is cut off.
- Political Pressure: The elected are asking the agency for accountability concerning the failures.
- Career Consequences: IT directors, managers, and administrators will risk their jobs.
Real-World Risk Examples
The critical consequences of non-compliance with CJIS Security Policy lead to real-world risks.
During a standard traffic stop, an officer without NCIC access due to non-compliance overlooked an active warrant. This escalated into a shootout, and the officer and suspect were injured.
In another incident for a 911 call, the dispatch couldn’t confirm the vehicle status, causing slow decisions and delayed backup. This gave an opening for the suspect to slip past security, prompting a high-risk pursuit.
Investigative units are also affected by non-compliance with CJIS Progress was hindered as they had to throw away evidence and criminal intelligence that was stored in non-compliant systems, which delayed a multi-agency drug probe.

Essential Benefits of CJIS Compliance for Police Operations
The benefits of CJIS compliance make police work run smoother and safer. When an agency is compliant, officers get full, reliable access to criminal justice databases without interruptions.
That translates into real-time warrant checks, vehicle lookups, and criminal history data when it matters most. In that sense, compliance isn’t just about avoiding penalties but also a smart investment that boosts operational performance, protects officers on the field, maximizes financial decisions, and improves the agency’s overall effectiveness.
Operational Benefits
The CJIS compliance benefits have a significant impact on the daily operations across police functions. The departments will experience the following:
- Uninterrupted database access: The officers get connected to NCIC, NLETS, and the state systems reliably with no interruptions, enabling them to do their mission-critical queries continuously.
- Officer safety enhancement: The real-time checks of warrants, the provision of gang affiliation data, and the issuing of officer safety bulletins are ways of providing immediate intelligence to protect those personnel who are in the field.
- Faster investigations: Detectives are able to get access to criminal histories, fingerprint matches, and case linkages instantly, enabling them to speed up case resolution from days to minutes.
- Improved dispatch effectiveness: The 911 operators can get critical details very quickly from their computer, which helps to improve accuracy and reduce interference caused by pressure.
- Mobile field capabilities: The patrol officers are able to query the databases while still in their vehicles or on their devices, supporting proactive policing without the need to go back to the headquarters.
- Inter-agency collaboration: The secure data sharing with partners from federal, state, and local sectors helps the smooth running of joint operations and multi-jurisdictional pursuits.
Security and Risk Management Benefits
Resilient CJIS standards strengthen the preventive barriers against contemporary threats, as they provide:
- Data breach prevention: Unauthorized external access to sensitive CJI is not allowed, as there are security measures in place to protect it.
- Insider threat mitigation: Criminal justice information is safeguarded against internal misuse due to the audit trails and role-based access controls.
- Cybersecurity posture: CJIS Security Policy is in complete alignment with NIST frameworks, providing the law enforcement industry with comprehensive protection that is specially created for its needs.
- Incident response readiness: CJIS requirements include incident response plans as cybersecurity countermeasures against emergencies to help efficiently detect, contain, and recover from breaches.
- Compliance documentation: Compliant agencies are always audit-ready with complete documentations that help them avoid liability during federal reviews.
Financial and Administrative Benefits
Compliance results in clear and quantifiable cost savings and improvements in regards to the financial situation and investments of the agency. Significant benefits are as follows:
- Federal grant eligibility: When you’re CJIS-compliant, you automatically fulfill a critical prerequisite of a lot of the funding programs, which means you have access to significant resources for training and proficiency development.
- Reduced liability exposure: Confirmed adherence leads to the minimization of lawsuits, fines, and the costs of remediation caused by data incidents.
- Vendor accountability: The CJIS Security Addendum holds software vendors legally responsible to adhere to CJIS requirements for their system’s security, reducing the burden for your administration.
- Streamlined audits: Well-organized records make the verification of compliance an easy routine rather than a disruptive ordeal.
- Insurance advantages: Insurers tend to cut down the cyber insurance premiums for CJIS-compliant agencies.
Public Trust and Accountability Benefits
Adherence to CJIS requirements significantly enhances the organization’s reputation among stakeholders. The departments create:
- Community confidence: The agency’s operations become more trustworthy to the public because of the secure way of handling personal data.
- Transparency and accountability: The extensive audit trails provide evidence for the proper use of CJI, effectively meeting the requirements for oversight.
- Professional reputation: The compliance indicates the commitment to the very best data security practices.
- Recruitment advantage: Modern, secure systems attract quality candidates and retain personnel as most prefer the latest tools that improve and simplify policing.
Long-Term Strategic Benefits
The importance of CJIS compliance extends to the future, not just immediate benefits. For forward-thinking agencies, continuous compliance is a necessary step in modernizing law enforcement. Compliance provides:
- Infrastructure for the future: Compliance supports the foundation for AI analytics and predictive policing tools by creating a secure and interoperable environment for emerging technologies.
- Interoperability: New tools and systems add-ons can be adopted smoothly, and no major renovation would be necessary.
Scalability: As agencies grow and data volume increases, compliant systems can easily expand and adapt without any hassle.

Core CJIS Requirements Every Police Software Solution Must Meet
Police software solutions need to fulfill the technical, administrative, and personnel CJIS requirements to guarantee security and compliance. This guide explains the mandatory CJIS standards for law enforcement to help agencies assess existing and prospective systems against strict CJIS standards.
Authentication and Access Control
To secure CJI against unauthorized access, agencies and software vendors apply rigid access controls to maximize data security.
All CJI access requires multi-factor authentication (MFA), which includes something you know (password), something you have (token), and something you are (biometrics).
As per CJIS Policy 5.6, strong passwords consist of a minimum of eight characters and require the use of uppercase/lowercase letters, digits, and symbols. Passwords shouldn’t be dictionary words, similar to user ID, or repeat previous passwords.
Police software also needs role-based access controls (RBAC) to limit access rights according to the position of the team member and the need-to-know principle.
Session management is also important to automatically log users out after a period of inactivity to protect sensitive data in case a device is stolen or left unattended.
On top of all that, agencies need to conduct access reviews every three months to check if user privileges correspond to their job roles.
Encryption and Data Protection
Criminal justice information (CJI) must be protected at every stage of its life cycle. That starts with encryption in transit, where all CJI transmissions are secured using TLS 1.2 or higher to prevent interception or tampering. Just as critical is encryption at rest, where any stored CJI must be protected with AES-256 or an equivalent standard, whether it lives in a data center, the cloud, or a local system.
Strong encryption also relies on reliable keys, which is why CJIS-compliant solutions also require secure key management, including protected storage, controlled access, and regular key rotation.
For officers and staff accessing systems in the field, mobile devices must use full-disk encryption to safeguard data if a device is lost or stolen. Finally, CJIS also requires secure disposal and media sanitization to make sure CJI cannot be recovered from retired hardware or storage media.
Audit and Accountability
Regular audits are a huge part of CJIS compliance. For this reason, the CJIS requires law enforcement software to implement comprehensive logging and tamper-proof audit trails.
Comprehensive logging makes it possible to track all CJI interactions, from access to modification to deletions. This requirement also includes log retention of a minimum of 1 year or more and searchable logs that can query and analyze access patterns, so your agency can obtain needed information quickly.
Meanwhile, tamper-proof audit trails serve as failsafe measures that prevent users from altering or deleting logs for data integrity and accountability.
Of course, these logs and audit trails need frequent log reviews with automatic alerts for suspicious access patterns.
Physical and Technical Security
CJIS compliance demands a secure hosting environment that protects CJI from both physical intrusion and cyber threats. Data centers should have strict access controls, surveillance, and monitoring that meet recognized security standards.
Network security must use firewalls along with intrusion detection and prevention systems to block unauthorized access and suspicious activity.
Beyond that, vulnerability management is equally crucial. Make sure operating systems and applications are regularly patched and kept current to close known security gaps. Combine this with configuration management to enforce hardened baseline settings and configurations.
However, something can still go wrong even with all these security measures in place. That’s why a CJIS-ready solution must support a well-defined incident response process that’s documented, tested, and ready to activate, so threats are contained quickly and operations stay reliable.
Secure environments are there to shield the CJI from both physical and cyber threats. Software solutions, on the other hand, incorporate these controls for dependable operations.
Personnel Requirements
CJIS compliance is based on personnel evaluation and formal agreements. Agencies keep records of these elements to stay ready for audits.
To screen the personnel for direct access to CJI, fingerprint-based FBI screening is used for the background checks.
Once they pass the background checks, trained, and sworn, all CJI users must undergo training in security awareness before they officially start with their duties. They must also take refresher courses every year.
A sanctions policy must also be implemented to govern personnel, clearly defining policy violations and their consequent penalties. Contractors and third-party personnel must also meet the exact requirements.
Administrative Requirements
To comply with CJIS, formal contracts and papers are necessary. Agencies need to ensure these rules are followed to be ready for audits.
First, the Security Addendum, which has to be signed by both the FBI and the state CSO. Second, the Information Exchange Agreements that set the rules for the sharing of data between the agencies involved.
Your agency will also need transparent policy documentation covering all 13 CJIS Security Policy areas to prove your understanding and compliance with CJIS requirements for law enforcement.
Lastly, to keep everything updated and verify proper compliance, conduct regular audits that consist of annual internal evaluations and state CJIS audits every 1-3 years.
Architecture Considerations
Modern designs make law enforcement software CJIS-compliant more efficiently. The different law enforcement agencies select architectures that do not pose risks, while supporting their operations.
These days, a zero-footprint design works best for law enforcement, as it leverages browser-based access to reduce the local attack surfaces.
Cloud systems have also seen an increase in adoption, mainly due to their efficiency, scalability, and lower maintenance needs compared to on-premise deployments. Although both can be CJIS-compliant, implementations vary in security controls, access management, and monitoring.
Moreover, modern police software solutions and operations demand multisystem integration, which is why API security has become a necessity, as it strengthens the interfaces for the smooth integration of systems.
Understanding CJIS requirements for law enforcement will guarantee that police software complies with the mandatory CJIS standards. This CJIS compliance guide for police software provides agencies with the necessary tools to pick solutions that ensure both security and efficiency in operations.

PsPortal: Purpose-Built CJIS-Compliant Infrastructure for Police Database Access
Purpose-built for CJIS-compliance right from its inception, PsPortals’ Portal XL and Personal Portal provide the foundational database infrastructure to access NCIC, NLETS, and state databases.
Portal XL and Personal Portal enable RMS, CAD, and other systems to securely query criminal justice databases. With over 30 years in the industry, PsPortals is trusted by law enforcement agencies nationwide.
Compliance by Design: How PsPortal Meets Mandatory Requirements
PsPortal meets the mandatory CJIS requirements through a system designed for law enforcement processes.
Authentication & Access Control
PsPortals have built-in multi-factor authentication that ensures all logins across the products are secure.
The detailed role-based access controls restrict access according to the roles of officer, supervisor, or administrator, while automatic session timeouts can be customized to fit agency-specific policies.
Not only that, PsPortals can be integrated with existing agency authentication systems, like Active Directory or SSO systems, without any hassle.
PsPortals in action is quite simple. An officer provides their login details along with the token to access criminal justice databases. The system then automatically logs them out after some time of inactivity. Access limitations become effortless.
Zero-Footprint Architecture
Browser-based Portal XL does not require any installations at the local level, significantly reducing the surfaces that can be attacked. This also means compliance advantages because no CJI is stored locally on workstations. All sensitive data is kept in secure data centers.
Portal XL simplifies auditing by centralizing logs of all accesses and activities with CJI and reducing scattered local files. Compliance updates are also centralized to deploy instant updates to all users in one go.
BYOD support allows police officers to access the databases through any compliant device. Agencies won’t have to replace their hardware completely.
Comprehensive Audit and Accountability
Every NCIC and NLETS query is automatically recorded with the user ID, timestamp, and details. Tamper-proof audit trails are then stored securely in a CJIS-compliant system.
And to further enhance audit-readiness and accountability, Portal XL has built-in automated alerts that detect irregularities such as multiple unsuccessful logins or access during off-hours.
With these features, along with searchable and exportable logs, agencies are always prepared for audits. They can export full logs in a matter of minutes during a CJIS audit and prove accountability and compliance.
Encryption and Data Protection
All data moving between systems are protected using TLS 1.3 encryption, while data at rest are secured with AES-256 for a complete end-to-end encryption that meets CJIS standards.
Psportals takes responsibility in managing encryption keys within its infrastructure, so you can rest assured. Zero-footprint architecture guarantees that there is no local CJI storage.
On mobile, the Personal Portal app fully encrypts all device-to-server communications, reducing data breach risks in the field.
So, when an officer in the patrol vehicle queries for warrants, the data traveling is encrypted, every action is logged, and no sensitive data is stored locally.
Product Suite for Mandatory CJIS Compliance
PsPortal’s tools have a direct impact on the central CJIS requirements.
- Portal XL (Browser-Based): Zero-footprint access to NCIC, NLETS, and state through any secure browser, centralized management and updates, and automated logging streamlines compliance.
- Personal Portal (Mobile): Compatible with iOS/Android to provide field database access with full encryption, MFA, and logging for field queries. Data on lost devices can be remotely wiped, and officers can securely run license checks at scenes.
- Testing & Certification Module: Administers NCIC operator certifications, monitors expirations, compliance reporting for audits, and restricts access to uncertified users.
- Super Administrator (Multi-Agency Management): Supports compliance management over a number of agencies, ideal for sheriffs with multiple jurisdictions. Unified audits and policy enforcement facilitate the operations between different jurisdictions.
Key Differentiators
PsPortal excels as a purpose-built CJIS compliance technology layer that agencies look for in mandatory access to databases. Law enforcement leaders choose it because of its proven reliability.
- Over 30 years of dedication to law enforcement: Comprehensive understanding of police operations and compliance requirements.
- Compliance expertise: Supports former law enforcement and CJIS experts.
- Continuous compliance updates: PsPortal technology is constantly updated to support the most advanced secure law enforcement software with CJIS compliance.
- Audit support: Direct help for preparation and documentation is given.
- Cost efficiency: The use of cloud eliminates the costs of on-premise hardware.
- 24/7 availability: Constant access to the database without any interruptions.
- Seamless interoperability: Works well with existing RMS, CAD, and case management systems.
Agencies validate these differentiators through vendor demos that emphasize the audit trails and zero-footprint access. PsPortal mitigates compliance risks while streamlining the operational process.
Operational Examples
Actual situations demonstrate the implementation of PsPortal’s compliance.
- Dispatch scenario: A 911 dispatcher checks NCIC warrants through the automatic logging of Portal XL access, the data is secured by encryption, and the logs ready for the audit are immediately accessible.
- Field scenario: An officer during a traffic stop makes use of Personal Portal for checks of the driver and vehicle, mobile encryption, and logging to comply with regulations.
- Audit scenario: IT team exports the complete PsPortal logs for state CSO examination, total accountability established, and audit clearance without any delays.
- Multi-Agency scenario: A task force of the county uses Super Administrator for a single monitoring over 12 agencies, which is in accordance with CJIS enforcement throughout the country.
Vendors are assessed by the agencies through the verification of purpose-built, for example, PsPortal CJIS compliance features.
To test the reliability of the compliance, begin with audit log demos and zero-footprint tests.
The PsPortal solution puts police departments in a position where the safety of officers, practical investigations, and hassle-free audits come as benefits.
Selecting CJIS-Compliant Police Software: Critical Evaluation Criteria
Agencies must put police software through a rigorous evaluation process to guarantee compliance with the CJIS standard, since federal mandates require evidence of compliance and not just vendor claims.
This CJIS compliance guide gives law enforcement leaders a clear framework to assess whether police software truly meets CJIS requirements.
Vendors that demonstrate built-in compliance by means of design and paperwork should be given priority, as this will ensure the protection of officers, the conduct of investigations, and dispatch operations. The best CJIS-compliant software is the one that fits into your current operations, lowers risk, and ensures reliable access to critical justice information over time.
- Verify Compliance Claims with Documentation
Insist on receiving a signed CJIS Security Addendum from the FBI, along with the reports of the third-party CJIS compliance audits.
Personally secure references from agencies in your state with different compliance requirements.
Red flag: Vendors who claim to be compliant but can not provide documents put agencies at risk of failing audits and going through interruptions in their operations.
- Evaluate Architecture for Inherent Compliance
For easier security management, prefer browser-based and non-installed solutions instead of installed software.
Verify that CJI storage does not use local devices to minimize the risk of breaches.
Check that updates are deployed centrally and that cloud data centers have strong physical security and redundancy to keep compliance up to date amid changing threats.
- Assess Authentication and Access Controls
Implement multi-factor authentication as a necessity, not as an option, and combine it with elaborate role-based access controls.
Ensure secure session management and automatic timeouts to prevent unauthorized access.
Carry out compatibility testing with agency authentication systems to secure operational efficiency.
- Examine Audit and Logging Capabilities
Implement a logging system that records the details of every CJI interaction, such as the user, the action performed, the time, and the location.
Insist on audit trails that cannot be altered and have retention periods that comply with state requirements.
Make sure audit logs can be exported and searched to support CJIS audits and demonstrate accountability.
- Review Encryption Standards
For communicating data, only TLS 1.2 or higher shall be used, and for storing it, AES-256 encryption will be applied, along with secure key management practices.
Check whether the encryption on mobile devices allows secure access to the fields. These standards avoid data interception, maintaining the integrity of the investigation.
- Evaluate Vendor CJIS Expertise
Review the vendor’s track record and experience serving law enforcement to confirm their reliability. Then, verify that they have devoted CJIS experts to help in the preparation of audits.
Ask for records and references from other agencies to confirm the vendor’s history of successful CJIS audits.
- Understand Total Cost of Compliance
Calculate initial setup, continual maintenance, upgrades, and audit assistance costs.
Identify any hidden costs, such as hardware or IT staff time. Transparent pricing signals a vendor’s commitment to long-term compliance.
- Assess Long-Term Compliance Maintenance
Find out how vendors track CJIS policy changes and take responsibility for keeping your system up to date.
Discuss agency liabilities in case of a change in requirements. Proactive vendors protect the business from possible interruptions in the future.
PsPortal and similar solutions are good examples of these criteria because of their purpose-built architecture, 30+ years of law enforcement experience, and complete compliance assistance, but agencies always confirm the claims with documents and references.
Common CJIS Compliance Mistakes Police Departments Must Avoid
To understand CJIS requirements, agencies need to recognize where mistakes commonly occur. These errors threaten database access and operations, but can be avoided with proper planning and awareness.
- Assuming “Cloud” Automatically Means Compliant
Cloud providers will be required to sign the Security Addendum and accept the mandatory CJIS standards for police purposes.
Check particular CJIS compliance documentation, not only general security certificates. Generic cloud services do not satisfy the federal requirements.
- Overlooking Third-Party Vendor Access
All transcription services, IT contractors, and backup providers are required to comply with CJIS.
Vendors involved with CJI will have to sign the Security Addendum, and there will be no exceptions for “indirect” access.
- Incomplete Background Checks
The law at the federal level necessitates the use of fingerprint-based FBI background checks for every person who has direct access to CJI.
State background checks alone are not enough. Every person with access to CJI, including contractors and civilian staff, must meet federal requirements.
- Inadequate Audit Logging
Access logs alone will not be sufficient. The CJIS standard necessitates logging of all queries along with a minimum one-year retention period.
Multiple systems may record logins, but may not have the detailed audit trails that federal auditors require.
- Treating Compliance as a One-Time Project
Continuous attention is a fundamental requirement of CJIS compliance. Changes in policy, personnel replacements, and new technology need ongoing monitoring and updates. Yearly training and periodic audits are also mandatory operational requirements.
- Failing to Secure Mobile Devices
Patrol devices (laptop, tablet, and smartphone) accessing CJI must fulfill overall CJIS specifications.
Remote wipe capability, encryption, and multi-factor authentication apply to all mobile access points.
- Not Preparing for CJIS Audits
Agencies often scramble during audits if they have not kept audit-ready documentation. Keep your policies, procedures, and audit logs organized and ready for immediate review.
- Selecting Software Based on Price Alone
Non-compliant services lead to substantial financial losses when access to the database is cut off. Evaluate mandatory CJIS standards for police, then go to features and pricing. Compliance is not negotiable.
These mistakes have a common link: they can be easily avoided through proper planning and checking of vendors. Agencies that address these weaknesses now are able to protect their database access and operational readiness before the audits arrive.
Budget Justification: Why CJIS-Compliant Software is a Mission-Critical Investment
Treating CJIS-compliant software as essential infrastructure helps police departments secure funding, maximize financial investments, and underscores why compliance is mandatory. Database access is critical for patrol, investigations, dispatch, and records management.
Non-compliant software does not cause minor issues. It results in a complete shutdown of police operations.
Mission-Critical Infrastructure:
CJIS-compliant systems are considered indispensable along with patrol cars, radios, and guns as the basic requirements for police operations.
Budget authorities approve these items because police work cannot continue without them. Access to NCIC, NLETS, and state systems is just as vital, since agencies and officers depend on this intelligence to function.
Risk Mitigation ROI
Compliance costs considerably less than the penalties of non-compliance.
Database access loss results in a stoppage of investigations, a risk to officer safety, and prevents warrant verification.
Data leakage incidents due to non-compliant systems cost up to millions in terms of remediation, legal penalties, and liability exposure.
The importance of CJIS compliance becomes clear when you compare the cost of compliant software to the losses from just one week without NCIC access.
Operational Efficiency Gains
The specialized purpose-built compliance systems have resulted in faster response to queries, lighter IT load, and better prepared audits.
These benefits translate into more resolved cases, safer officers, and time saved for administration, providing greater value than trying to manage compliance on your own.
Financial Advantages
Compliance with CJIS permits access to grants from both the federal and state governments. In addition, many funding programs have compliance as a prerequisite for receiving the money.
Portal XL and similar cloud-based solutions eliminate the need for expensive local infrastructure, constant hardware upgrades, and dedicated IT staff.
Changes in compliance managed by the vendor cost less than the management of compliance by internal management.
Budget Comparison Framework
Perform a cost comparison between the compliant software investment and the operational costs during a database access suspension. In just one week, you’ll find out that the price of regulatory software is trivial in comparison to the cost of a week’s database access loss.
Policing is simply impossible without database access. It can be costly not just to your agency and officers but also to the public.
Frequently Asked Questions About Mandatory CJIS Compliance
Why is CJIS compliance mandatory for all police software?
CJIS compliance is a must since federal statutes command the safeguarding of CJI, which is made available via systems like NCIC. The reason for making CJIS compliance mandatory originates from the 28 U.S.C. § 534 law, which obligates the secure management of national crime databases.
What happens if our police department uses non-CJIS-compliant software?
The non-compliant software causes an instant NCIC database lockout, stopping operations related to investigations, warrants, and officer safety checks, resulting in complete disruption until the issue is fixed.
How do we verify a police software vendor is truly CJIS compliant?
Ask for the signed CJIS Security Addendum, examine their FBI authorization letter, and compare their policy documents with police-mandatory CJIS standards. Do vendor reviews every three months.
What is the best CJIS compliance solution for police departments?
PsPortal provides the most reliable CJIS compliance solution for police, as it has a secure database access infrastructure layer designed explicitly for the PsPortal CJIS obligatory compliance software, meeting the law enforcement software CJIS requirements without reconstruction.
Does CJIS compliance apply to cloud-based police software?
Yes, it is necessary for cloud service providers to execute the Security Addendum and comply with all controls and check the FBI’s authorization, since standard cloud security is not adequate.
How much does CJIS-compliant police software cost?
Different agencies have different prices, and the typical range is from $5K to $50 per year. Still, compliant systems provide ROI by preventing downtime and reducing remediation costs, which are more than $500K per breach.
How often do police departments get audited for CJIS compliance?
Federal audits happen every 3 to 5 years. Moreover, state or local examinations and inspections that are initiated keep the facility in an audit-ready status by performing self-assessments yearly.
Why CJIS compliance is mandatory isn’t a complicated question. Federal law makes it a must. The FBI allows access to the national crime databases with the condition that the agencies safeguard that information by implementing extensive security controls. Those security controls are CJIS standards.
The consequences are very serious. Defying the rules leads to instant termination of database access, no delay, no gradual process, just immediate termination. Law enforcement activities become impossible, the safety of police personnel is compromised, and the quality of service to the public is reduced.
Purpose-built solutions matter. The use of general-purpose software with retrofitted CJIS compliance features leads to constant risks and management challenges. Software designed for law enforcement, like CJIS-compliant PsPortals, makes compliance easier and reduces risk.
Compliance is an investment in operational capability rather than only a regulatory obligation. A safe and reachable database infrastructure allows the police to be effective and accountable. Police work more safely. The detectives are quicker in their work. The people are served better.
Don’t wait for an audit or a database lockout to review compliance. Audit your systems now, verify your vendor’s compliance, and select solutions built for your agency’s needs.
Get in touch with PsPortals right away. Your agency and staff deserve infrastructure designed for compliance from the start.